The results posted below may not necessarily match actual vendor compatibility results taken elsewhere. Also, a complete testing of all possible combinations was also not made during this testing. Thus network configurations should not be planned around the test results listed below, so network managers should pre-test final configurations prior to assuming that they will be as per the results listed below.
One last word, as versions are constantly being revised, please be aware that the results posted in this test are only valid for the versions which were tested and may not necessarily match the results of the latest version.
Testing Method
NTT's 3rd IPSec Interoperability testing has been broken into two (2) steps to test interoperability amongst all products. (Due to time limitations, some products were unable to be fully tested.)
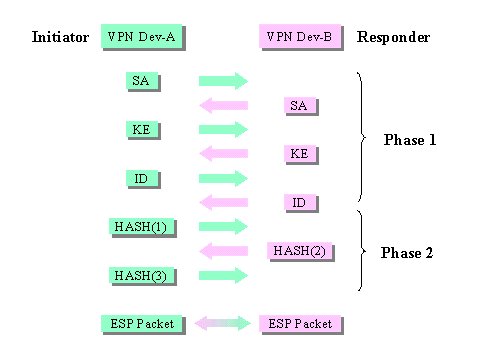
Step 1 1. ICMP Pings were sent by the Initiator on one side of the VPN to the Responder on the other side of the VPN. 2. To ensure proper transition from Phase 1 to Phase 2 (SA establishment), the IKEVIEW Analyzer was used to log and debug troubles which occurred. 3. The Initiator and Responder roles were then reversed to confirm proper sequencing in the other direction as well. 4. Only when both Initiator and Responder roles were completed would the testing continue with Step 2. Normal Operational Sequencing for Step 1 *Some Notification and HASH Information are include as well.
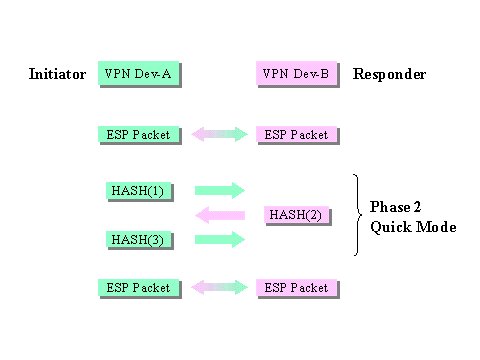
STEP2 1. Set the [SA Lifetime] on one side to a very short time span. 2. Set the [SA Lifetime] of the other side longer than the short lifetime specified in 1. 3. The VPN device set with the short [SA Lifetime] will then timeout and re-key with the VPN device set with the longer [SA Lifetime] while continuous PINGs are sent across. 4. Proper [Re-key] sequencing after the SA Lifetime has expired will be confirmed by using the IKEVIEW Analyzer as well as referring to the various logs and/or diagnostic tools of each device. Normal Operational Sequencing for Step 2 * After [Re-Key] sequencing has completed, a new SPI and Sequence Number should be assigned. ** Notification or other HASH Informational information may also be transmitted as well.
Network Configuration
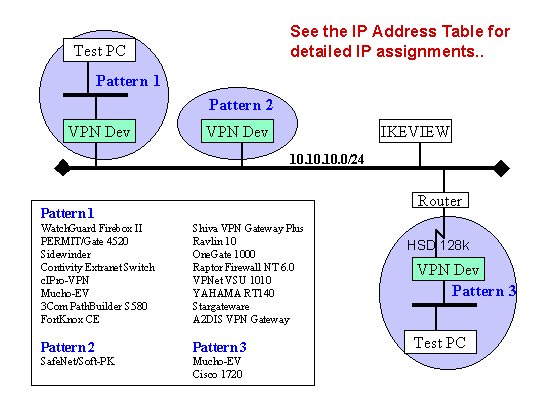
IP Address Table
(Actual IP addresses used for testing)
Device Name Global IP
AddressIP Address of the
Gateway for that devicePrivate IP
AddressPrivate PC
IP AddressWatchGuard Firebox II 10.10.10.1/24 - 192.168.1.1/24 192.168.1.2 Shiva VPN Gateway Plus 10.10.10.2/24 - 192.168.2.1/24 192.168.2.2 PERMIT 10.10.10.3/24 - 192.168.3.1/24 192.168.3.2 Ravlin 10.10.10.4/24 - 192.168.4.1/24 192.168.4.2 Raptor Firewall NT 10.10.10.5/24 - 192.168.5.1/24 192.168.5.2 Sidewinder Security Server 10.10.10.6/24 - 192.168.6.1/24 192.168.6.2 Contivity Extranet Switch 10.10.10.7/24 - 192.168.7.1/24 192.168.7.2 OneGate (FreeGate) 1000 10.10.10.8/24 - 192.168.8.1/24 192.168.8.2 cIPro 10.10.10.9/24 - 192.168.9.1/24 192.168.9.2 VPNet 10.10.10.10/24 - 192.168.10.1/24 192.168.10.2 Mucho-EV (1) 10.10.11.1/24 10.10.10.248 192.168.12.1/24 192.168.12.2 YAMAHA RT140e 10.10.10.13/24 - 192.168.13.1/24 192.168.13.2 Cisco 1720(1) 10.10.12.1/24 10.10.10.254 192.168.14.1/24 192.168.14.2 A2DIS VPN Gateway 10.10.10.15/24 - 192.168.15.1/24 192.168.15.2 PathBuiler 10.10.10.13/24 - 192.168.16.1/24 192.168.16.2 SafeNet Soft/PKI 10.10.10.17/24 - 192.168.17.1/24 192.168.17.2 Mucho-EV (2) 10.10.15.1/24 10.10.10.250 192.168.23.1/24 192.168.23.2 Cisco 1720(2) 10.10.16.1/24 10.10.10.253 192.168.24.1/24 192.168.24.2 OCN Business Pack
VPN(FortKnox)10.10.10.27/24 - 192.168.27.1/24 192.168.27.2 STAR-Gateware 10.10.10.28/24 - 192.168.28.1/24 192.168.28.2
* The default gateway for 10.10.10.0/24 is 10.10.10.254.
* Devices connecting via HSD to the router use an Unnumberd IP.
* SafeNet Soft/PKI was tested with and without the Private IP Address set.